Email is one of the most direct and effective channels for connecting with your customers. You can build strong customer relationships with your email campaigns. Like most brands, you might be using an email provider platform to send your carefully crafted promotions to your customers.
As a marketer, while you may be busy with your day-to-day activities of crafting content, monitoring metrics, and keeping track of KPIs, you should also be focusing on the security details of your platform. The more information you get from your provider on your data safety the more secure you will feel.
At Netcore, we always go above and beyond in ensuring that your emails are end-to-end secure and your customer data is safe. Security and privacy are central to all we do. We’ve built data protection right into the product design, knowing the importance of customer data security, right from the beginning. Our team is dedicated to building robust security tools to safeguard our platform from malicious attacks, while we continue to deliver exceptional value with our cutting edge AI-powered platform features.
You can be rest assured that right from the process of email creation to its transition between servers and finally, even after delivery, your information contained in the email remains secure and intended only for your recipients. At Netcore, we have specialized teams to build, scale, and maintain email infrastructure. To keep our customer data safe is our top priority and is part of our values and culture.
Unlike other providers, you will never face the same issues with your authentication and security. All our teams are provided with information security training and are trained to identify security risks and mitigate them. We strive to make sure that our customers don’t have to worry about their data security on top of everything else on their plate.
Here are some important security features that we use to guarantee that right from inception to last-mile delivery, your email data is encrypted and secure.
1. Account security
- Multi-factor authentication (2FA)
Two-factor authentication eliminates anyone else getting your credentials and having access to your account. The authentication code is shared via email OTP or google authenticator. It is a functional multifactor authentication system with no loophole like some other providers with a faulty SMS option.
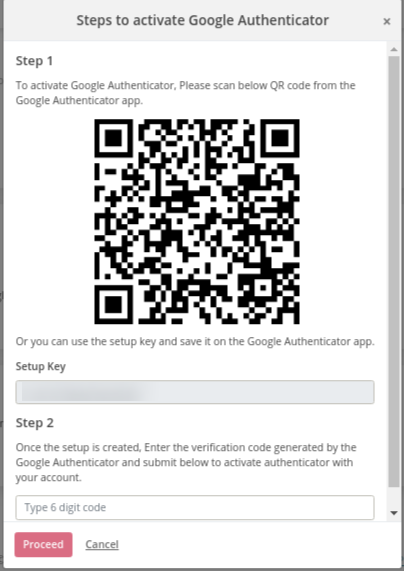
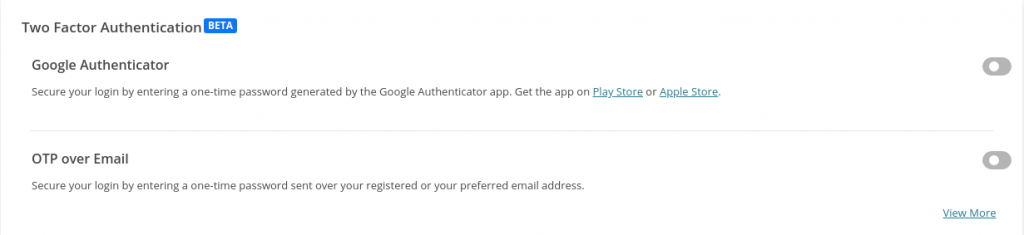
Benefit:
A one-time authentication code will provide the control of the account solely to the person with the credentials and eliminates the risk of any third party getting access.
- IP bound custom API keys
Until now, our customers had access to an API key that could be shared across applications. However, with the new update, you can create custom API keys that are bound to specific applications and sets of IP addresses. A request generated from any other IP will be blocked. This creates a secure API key that you can use with your specific applications if you have a set of IP addresses that your applications work on.
Benefit:
The secure key helps you to access your set of applications and not worry about anyone getting hold of your API key to take over all the applications running on the account.
2. Data security
- TLS enabled email transition
Our mailing servers enabled TLS (Transport layer security) on all emails before they are sent out. TLS uses encryption for your message while it is in transit between the sending and receiving server. TLS prevents eavesdropping on emails or any MIM (Man in the Middle) attacks on your emails as it is being carried between servers.
All our API endpoints and SMTP injection servers support HTTPS and TLS respectively ensuring your emails are accepted and delivered securely. We also make sure that digital certificates and public key infrastructure are used in TLS encryption. This process verifies that the sender server is a genuine source, which helps to prevent spoofing.
Benefit:
You can trust that your emails will be encrypted with the latest technologies, with the transition, and the last-mile delivery will be secure. In addition, there will not be an issue of a third party modifying your email contents between transitions, preventing any phishing or spoofing attempts that can be carried out by attackers.
- Email encryption at rest
Encryption allows the user to encrypt the PII (Personal Identifiable Information) of the recipient.
What is PII?
PII is any data that one could potentially use to identify a person associated with said data.
In the context of data breaches and identity theft, PII is the most sensitive data point. Therefore, we should keep the exposure of PII to a minimum. The awareness of safeguarding PII has undoubtedly increased in the last few years; however, it has mostly been within the confines of the organization. Any particular brand still interacting with several partners/vendors, exposes their PII data to potential misuse.
What information is encrypted?
We use SHA-1 to convert the email address, recipient name (and any other recipient’s PII information) to a hash value and store the value instead of original data for 90 days.
In the image above, you can notice that the email addresses are visible in the logs. However, once encryption is enabled, the email addresses are replaced by the encrypted hash value.
Benefit:
As the email ids will be converted to encrypted hashed values, they will not be visible to any third party in case they get hold of this data. As such the encrypted data cannot be used for any potential misuse in the hands of an attacker.
3. Application Security
- Webhooks with HMAC authentication
Using Webhooks, we provide you with full control of your email activities. You will be able to configure webhooks/callback URLs for each of the events like delivered, opens, clicks, unsubscribe, bounce, etc.
You will get immediate answers to your most pressing questions on email delivery and engagement such as:
- Was the email successfully delivered to the recipient’s inbox or did email delivery fail?
- Did the email bounce? If so, was it a soft bounce or a hard bounce?
- Was the email opened?
- Did the recipient click within the email?
- Did the recipient unsubscribe?
We offer you an authenticated mechanism to keep your Webhooks secure. We use a hash message authentication code (HMAC) using which you can use to verify and authenticate the incoming message. In this case, a secure code will be shared with the email sender and then the webhook will be encoded using HMAC. Only the shared code can decode the hashed crypto code sent to the email sender.
Benefit:
Now you can track your responses in real-time using our secure webhooks. You won’t have to worry if the messages coming to you are legitimate as they will be encoded using HMAC and no one else can decode them except you.
Apart from data security, our customer support is one of the best in terms of query satisfaction in a timely manner. You’ll never have to wait long for a response regarding your query.
Your Security is our Promise to You
In today’s times, customer data is a precious and valued commodity. Email has become one of the primary channels for phishing, spoofing, and other cyber attacks. Your business depends on the way you secure it and keep sensitive information away from attacks.
If your business engages in email marketing, then your email content needs to be secure with either your in-house platform or email provider. If this data is compromised then you will lose your customers’ trust.
Your email program needs to be encrypted from injection to the inbox of the recipient. Also, no third party should gain access to your account which needs strict authentication protocols.
A marketer needs to prioritize the best security for the data they store with the platforms. Netcore’s security features with Account, Application, and Data Security, will enable you to focus on your email program and leave the security and privacy of your data to us.
If you are not happy with your current platform, then it’s time to pick a solution that’s superior in technology and security, like Netcore.
Get in touch with the Netcore experts today to learn more details.