What Are Email Blacklists? How to get a domain or IP address Delisted?
Published on 2020-04-11· Updated on 2024-04-10
Introduction
Getting your email ID into an email blacklist is the most critical root cause of email deliverability issues. Once the domain or IP address is on the blacklist, you'll notice an immediate uptick in emails reaching to spam folders and bounce rates. These detrimental effects can severely impact your brand reputation and lead to a severe decline in email open rates. Thus, employing an Email Blocklist Checker becomes indispensable for all those who use email as a marketing channel.
Email blacklisting can happen in two ways: The IP address of the sending mail server or the domain name of the sending email address gets into the blacklist. While crafting compelling customer-engaging content is undoubtedly vital, sending emails to relevant and verified users is equally crucial. Neglecting email best practices can lead to blacklisting. Sending emails from a blacklisted domain can result in significantly reduced email deliverability rates. Prominent global mailbox providers such as Gmail, Yahoo, and Outlook often discard emails originating from blacklisted sender domains and assign them a negative reputation score.
In this tutorial, you will learn A-Z of email blacklisting and how to get your domain and IP off the list.
Here’ s what we'll cover:
FAQ
- What is an email blacklist?
- Types Of Email Blacklist Services
- Email Blacklist Categories
- Who Influences The Email Blacklist?
- How does DNSBL work with the MSP and ISP?
- What Are Some Signs Of Being Blacklisted?
- Check Domain Blacklist In Real-Time
- How Do I Know If My Emails Are Blacklisted?
- Behavior That Gets You Listed In Email Blacklist
- How do I get my email off the blacklist?
- How Do I Stop Being Added To Email Blacklist?
What is an email blacklist?
An email blacklist, also known as DNSBL (Domain Name System-based Blackhole List) or RBL (Real-time Blackhole List) is a large list of public domains and IP addresses that are marked to be suspicious for sending spam emails over the internet. Entities like ESP (Email Service Providers), ISPs (Internet Service Providers), and ASA (Anti-spam agencies) refer to this list to detect and block any spam emails from entering their network.
There are over 300 known email blacklists that anyone can access - some of them have a bigger impact than others on email deliverability.
DNSBL, or email blacklist, is not a single centralised list on the internet. Many anti-spam organisations are maintaining their independent DNSBL lists. Some of these lists are free to use, while few require commercial licenses.
What are the types of email blacklist services?
There are two kinds of Email Blacklist Services:
- Third-party email blacklist services
These are independent organisations that provide blacklists as a service to email clients such as Gmail, Yahoo, Email delivery services, Spam engines, etc. These are widely available and open for the public to check their listings manually for free.
We have listed some of the most popular email blacklist databases that you can use to check if your domain or IP is blacklisted. Apart from blacklisting services, they also provide several security-related services.

List of popular email blacklist databases
Here are some of the most popular ones to look up your IP or domain name:
- Composite Blocking List (CBL)
- Senderbase
- Spam and Open Relay Blocking System (SORBS)
- Spamhaus Block List (SBL)
- XBL Exploits Block List
- Spamcop
- Passive Spam Block List (PSBL)
- Invaluement
- Barracuda
- SenderScore
Most of these blacklist databases of IP addresses and domains also include the addresses of known spammers, open SMTP relays, proxy servers, and zombie computers.The Internal Email Blacklist Service
Although Gmail, Yahoo might use these third-party services to check to blacklist, they also have their own filters to update their version of blacklists. These internal blacklists are not so much as open to the public users to use without any verification.
2. Internal email blacklist service
Although Gmail and Yahoo might use these third-party services to check blacklists, they have their own blacklist filters as well.

These services store blacklists in different categories. Let's check them out.
What are the email blacklist categories?
An email blacklist is divided into two categories depending on the spamming source.
- IP Blacklist - Every server has an IP address that defines its location on the internet. The public IP addresses of the servers that are known to send spam emails are infected with botnets or acting as an open relay and are added to the IP blacklist. If a user sends spam emails from their private IP address continuously, their IP addresses can be blacklisted too.
- Domain Blacklist - Every email that you send has a domain associated with it, and it’s called the email-sending domain. If the email contains any spam elements (such as spammy words or suspicious links) or is reported several times as spam by email recipients, such email-sending domain is blacklisted. The sending domain can be seen in the From-address, Return-address, and also in the DKIM signing domain.
Note: Apart from the spam issues, email recipients can also blacklist any “no-reply email domain.” This happens when brands send marketing emails from a no-reply email address without the recipient’s permission.
The emails sent by the domains that are considered spam—based on the sending habits and history of emailing—are added to the email blacklist.
The process of permanently removing your email from a blacklist involves more than simply requesting removal and having your email delisted. Attempting such an action without a comprehensive strategy can lead to re-listing, making subsequent removal an even more challenging task. First, understand the root causes to address and resolve email blacklisting issues. Also, identify the key authorities, entities, and influencers responsible for listing your domain or IP address on a blacklist.
Who Influences The Email Blacklist?
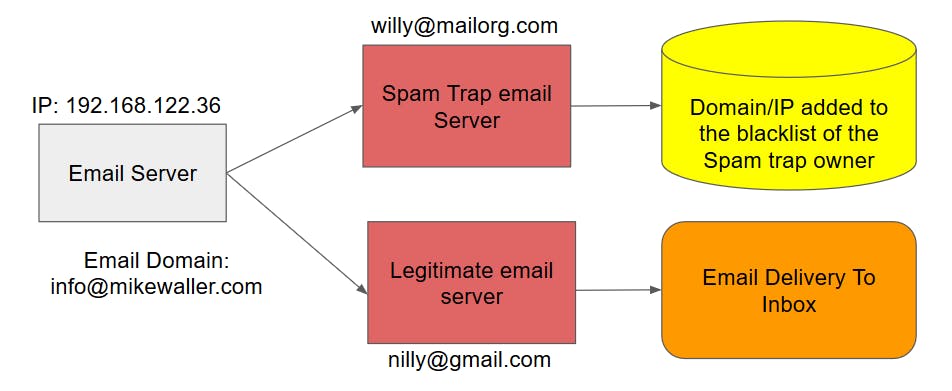
It's crucial to recognise that, even when sending high-quality emails, a minor oversight can result in your domain being blacklisted. Using non-opt-in email lists procured from external sources is a good example. In such instances, there is a significant likelihood that your list contains spam trap (honeypot) email addresses. Inadvertently sending emails to these spam trap addresses can lead to your sending domain and IP address being blacklisted across multiple DNSBL services.
MSPs, ISPs, Anti-Spam vendors, and even the recipients of your email can influence the blacklisting of email sender domains or IP addresses. Let’s understand these scenarios one by one.
1. The Mail Service Providers (MSP)

MSPs are the email services that provide inboxes like Gmail, Yahoo mail, Outlook, Zoho Mail, etc. These services diligently monitor their email traffic for suspicious and spam emails and take action against any sender, whether it’s an ESP or an individual.
2. The Email Recipient
These are passive influencers in the email blacklisting. The open SMTP (Simple Mail Transfer Protocol) allows for the transmission of emails without inherent protocol-level checks or restrictions. This process makes it challenging to detect and filter all forms of spam.
To combat spam, most MSPs offer a "Report as spam" button, functioning akin to an open poll. When a sufficient number of users flag an email as spam, there is a likelihood of the sender's domain being added to a blacklist. This mechanism underscores the importance of adhering to best email practices and delivering content that resonates positively with recipients.
3. Spam Traps or HoneyPot Email Addresses
These email addresses closely resemble standard email addresses and are predominantly owned by anti-spam agencies and MSPs. They strategically disseminate these trap email addresses across the internet to monitor any unsolicited email activity. It's important to note that a significant portion of harvested or third-party email lists would inadvertently contain a few of these spam trap email addresses.
Engaging with even a single spam trap can have immediate repercussions, potentially resulting in real-time blacklisting of your sender domain and IP address. Exercise utmost caution and adhere to email best practices to safeguard your email sender reputation.
Spam traps are mainly grouped into two categories.
(a) Classic spam traps: The traditional or longstanding spam trap email addresses used by anti-spam agencies and email service providers to identify and combat unsolicited and potentially malicious email activity.
(b) Recycled spam traps: The email addresses that were once legitimate but have been abandoned by their original users and subsequently repurposed by anti-spam organisations as spam traps. When marketers continue to send emails to these recycled spam traps, it can lead to email blacklisting or damage the sender reputation.
4. A Sudden Increase In Email Volume
Rapidly escalating email volumes can serve as a red flag, indicating the use of bulk email lists procured from external sources. The logic is natural: How is it possible to gather such an extensive subscriber base overnight?
In today's landscape, the email marketing industry exercises a significant degree of control over email blacklisting. By employing DNSBL services and applying their own stringent blacklisting criteria, they encourage best practices.
DNSBL service transcends being a mere catalogue of domains; it functions as a comprehensive software ecosystem that seamlessly integrates with ISP’s DNS infrastructure. This infrastructure is responsible for mapping IP addresses to domain names and vice versa.
What happens once your domain/IP is blacklisted? Does all email communication come to a halt until delisting occurs?
The answer hinges on a complex interplay involving MSPs, ISPs, and internet mailing services. It needs a closer look at how these entities engage with DNSBL and handle emails originating from blacklisted domains and IPs.
How Does DNSBL Work With The MSP and ISP?
Every MSP and ISP employs one or more DNSBL services to detect and categorise blacklisted emails. These services can be configured either locally within their infrastructure or accessed remotely through a connection. Regardless of the setup, the DNSBL service uses the local DNS server to perform domain-to-IP mapping, effectively identifying and categorising incoming emails.
This empowers MSPs to proactively intercept incoming spam at the Mail Exchange (MX) server entry level. By doing so, they safeguard the integrity of their entire email infrastructure and protect recipients' mailboxes from being inundated with spam. The MX server promptly rejects these unwanted emails and issues a bounce-back message to the sender's address based on the server's predefined policies.
What are the email policies?
Each ISP and MSP operating on the internet implements proprietary algorithms to manage email spam. It's important to note that encountering delivery issues with one MSP, such as Gmail.com, does not necessarily imply the same challenges will arise with another MSP, like Yahoo.com.
Some providers promptly blacklist the sender and begin discarding the email, specifying a particular bounce reason code. In contrast, others opt not to blacklist but instead employ a bounce code to reject the email.
It's critical to act on incoming bounce notifications in real-time. Different bounce reasons require different levels of effort to resolve:
- If the bounce is due to blacklisting, then you might have to suspend your email program and re-examine the email list and what you were sending.
- If the bounce is around email throttling, you will have to slow down your email sending volume.
- If the bounce code is tagged as hard, you should remove the associated email address immediately from your list as it’s invalid.
MSPs and ISPs believe in fighting spam together, and they are open to sharing reasons for bounces. If you are not taking immediate action on these bounces, it signals that you are not being compliant with the email sending guidelines.
Here is a flow diagram that explains the process followed by ESPs to filter blacklisted emails.
The sender IP is matched against the blacklist, and different actions are performed based on the response and policies:
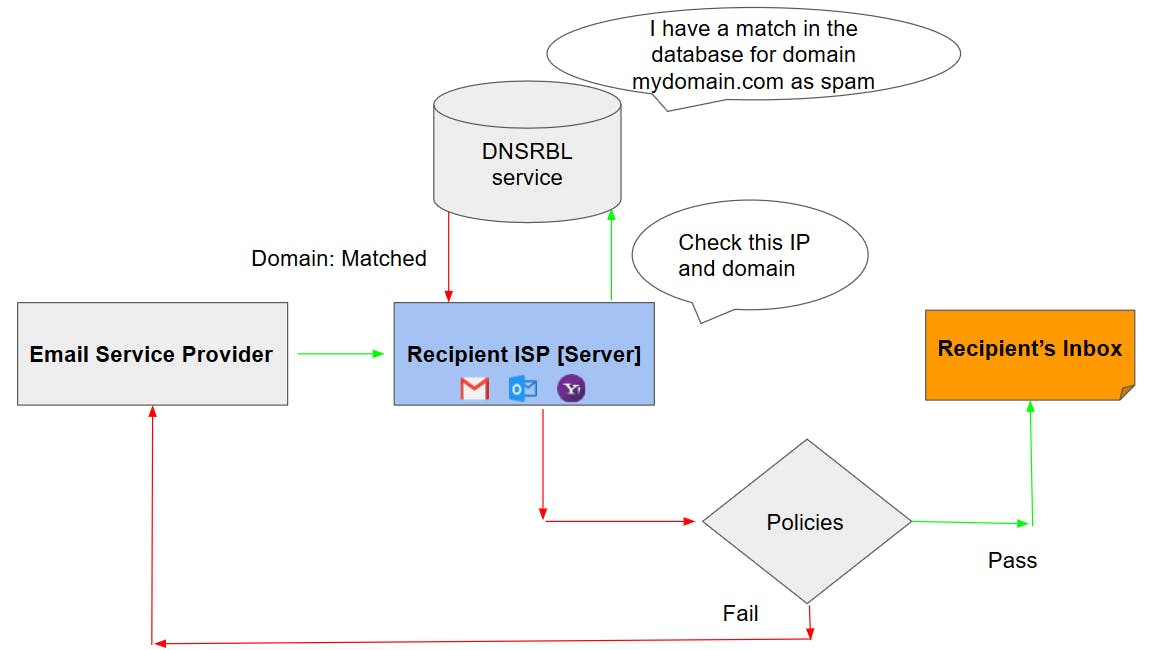
- The message is rejected and bounced back to the sender address with notification
- The message is accepted to be sent to the inbox
The policies for email filtration depend upon the respective ISPs.
How ISPs use their internal email blacklist?
Every ESP, including Gmail, Y-mail, and Outlook has a domain reputation list that would mark you as a good or bad sender. This is based on your email activity and sending domain reputation. For example, Gmail provides a tool called Google-Postmaster for checking the domain reputation. Based on the reputation, the action on the received email (sent to the inbox or spam) is decided by the Gmail ESP.
Other ISPs too have their reputation list and blacklist, but you will only get notifications regarding emails being dropped as warnings. Their reputation lists are not accessible to the public right now, but you can expect it in the near future.
Getting on an ISP's own blacklist can be a bigger problem than ending up on third-party lists. This is because ISPs have strict spam-filtering rules. Major email services like Gmail, Yahoo, and Outlook reach a lot of people worldwide, so it's crucial to follow their rules to ensure your emails get to the inbox.
When you are blacklisted by any email blacklisting service or a ESP you will receive a notification through an email or bounce alert email to your return address.
If you're not receiving notifications, watch for subtle signs that might indicate you're blacklisted.
What are some of the signs of being blacklisted?
If you are blacklisted, you won’t be able to send emails to the recipient’s mailbox. Most of the time, it will be dropped at the recipient’s MX server and return a bounce code. But does that mean you will be blacklisted from every mail server?
No.
Even if you are blacklisted on a particular DNSBL service, there are hundreds of other email blacklists on the internet. Non-delivery of your email depends upon whether the recipient’s server is referring to that particular DNSBL that blacklisted you.
However, MSPs can have email filtering mechanisms other than blacklists to filter out spam emails.
For example, few MSPs consider your previously sent emails and their engagement as the key parameter to classify or reclassify if your domain/IP is blacklisted.
Here are some instances that showcase that your domain or IP might be blacklisted:
- Increasing dropped emails
- Deteriorating delivery rates
Once you notice these signs, you can go ahead and check if your domain and IP is blacklisted.
How to check domain blacklists in real-time?
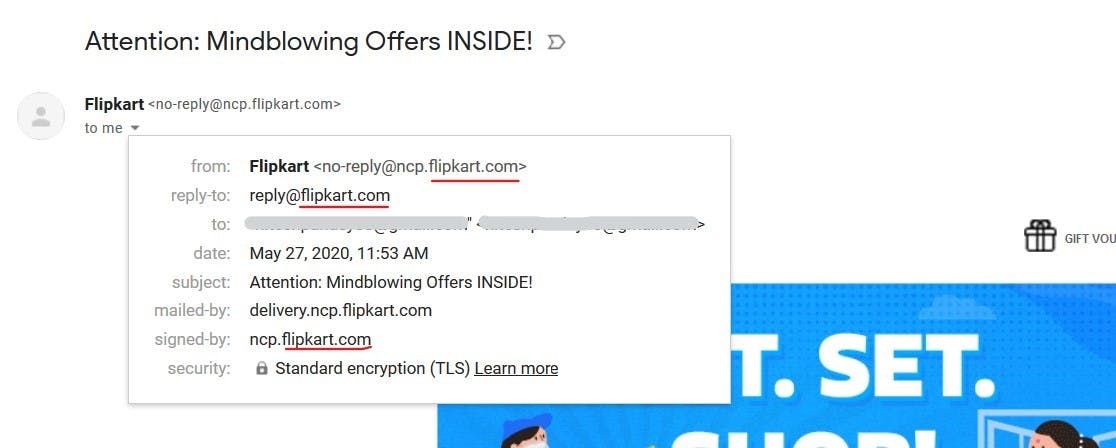
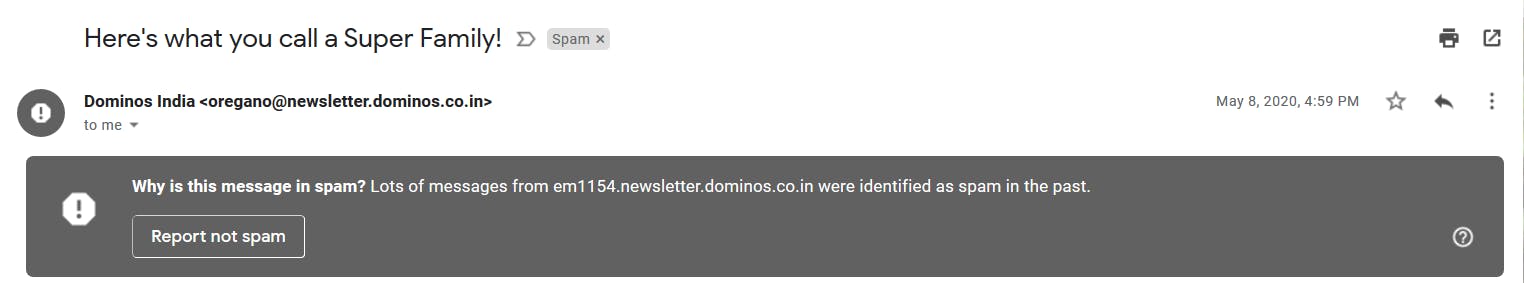
The blacklist checker will scan an IP address or domain in over 200 DNSBLs or RBLs. If you don't know the IP address used for sending your mails, check the email headers of a few emails to get an idea (as shown in the image below).
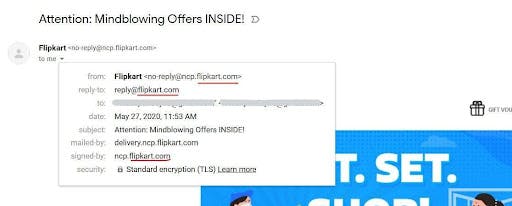
If your domain or the mail server's IP address has been blacklisted, there is a high chance that some of the emails that you had sent may not have been delivered.
How to know if your emails are blacklisted?
Checking for some of the obvious signs that you are blacklisted as mentioned in the above is one way. The other two ways are as follows:
- Check bounced emails
Many major blacklisting services and ISPs include SMTP error codes in bounce-back emails, offering insights into the blacklisting reasons. Services, such as Spamhaus, provide a panel where SMTP errors for your domain can be reviewed after signing up. Alternatively, you can also check these SMTP errors in your email server's log. Below are examples of bounce-back emails from Yahoo, Gmail, and Outlook, caused by internal blacklisting.
- Yahoo!
August 16 17:38:04 messagerie-prep postfix/error[12137]: 54B5B64010C: to=<[email protected]>, relay=none, delay=17397, delays=17397/0.02/0/0.03, dsn=4.4.1, status=deferred (delivery temporarily suspended: connect to mx-eu.mail.am0.yahoodns.net[188.125.69.79]:25: Connection timed out)
August 16 17:43:09 messagerie-prep postfix/smtp[12502]: BFC8564010F: to=<[email protected]>, relay=mta6.am0.yahoodns.net[98.136.101.117]:25, delay=1128, delays=1123/0.08/4.5/0.23, dsn=4.7.0, status=deferred (host mta6.am0.yahoodns.net[98.136.101.117] said: 421 4.7.0 [TSS04] Messages from 197.201.1.54 temporarily deferred due to user complaints - 4.16.55.1; see Error: "421 4.7.0 [XXX] Messages from x.x.x.x temporarily deferred due to user complaints - 4.16.55.1" when sending email to Yahoo
2. Gmail
August 13 11:07:09 messagerie-prep postfix/smtp[11924]: 4E415641FD5: to=<[email protected]>, relay=gmail-smtp-in.l.google.com[173.194.76.27]:25, delay=4.7, delays=0.06/0/0.41/4.3, dsn=5.7.1, status=bounced (host gmail-smtp-in.l.google.com[173.194.76.27] said: 550-5.7.1 [197.201.1.54 19] Our system has detected that this message is 550-5.7.1 likely suspicious due to the very low reputation of the sending 550-5.7.1 domain. To best protect our users from spam, the message has been 550-5.7.1 blocked. Please visit 550 5.7.1 Why has Gmail blocked my messages? - Gmail Help for more information. 91-v6si6257010wrg.38 - gsmtp (in reply to end of DATA command))
3. Outlook
August 16 16:39:06 messagerie-prep postfix/smtp[8006]: 346B56400E6: to=<[email protected]>, relay=none, delay=260903, delays=260840/0.01/63/0, dsn=4.4.1, status=deferred (connect to eur.olc.protection.outlook.com[104.47.6.33]:25: Connection timed out) May 16 16:48:33 messagerie-prep postfix/smtp[8708]: connect to eur.olc.protection.outlook.com[104.47.14.33]:25: Connection timed out
Check your IPs and domains in email blacklist directory
If you think to check your email blacklisting in the 10 or so RBL service is enough, then you are wrong. There are hundreds of different kinds of email blacklist services on the internet. Checking manually in all of these services isn't a practical solution and will take days to check in all of them, considering you do know all of the services.
To save your precious time there are services on the internet that maintains a list of live RBL directories to lookup your domain/Ip address and check if you are listed or not. They even provide a page dedicated to that particular RBL service detailing types of RBL list they use and some links to help you delist your domain/IP address.
Here is a list of the popular lookup tools to check the domain blacklisting on various DNSBL lists:
Checking your email blacklisting in the top 10 RBL services is not enough - there are hundreds of email blacklist services on the internet. Checking manually in all of these services isn't practically possible.
Use the services that maintain a list of live DNSBL directories to lookup your domain/IP address to check if you are listed in them. They even provide a page dedicated to specific DNSBL services with the types of DNSBL list. They also share recommendations to help you delist your domain/IP address.
Here is a list of the popular lookup tools to check the domain blacklisting on various DNSBL lists:
1. emailDojo blocklist checker: This is a free community tool that checks your domain across 100+ global blocklists. It highlights the blacklist status and also suggests ways to get delisted. You can also get ongoing alerts set up for your domain in real-time for free.
2. MultiRBL: This is a free site that scans on 100+ DNSBL lists to check for domain blacklisting. It also shows the steps to remove your domain from the blacklist.
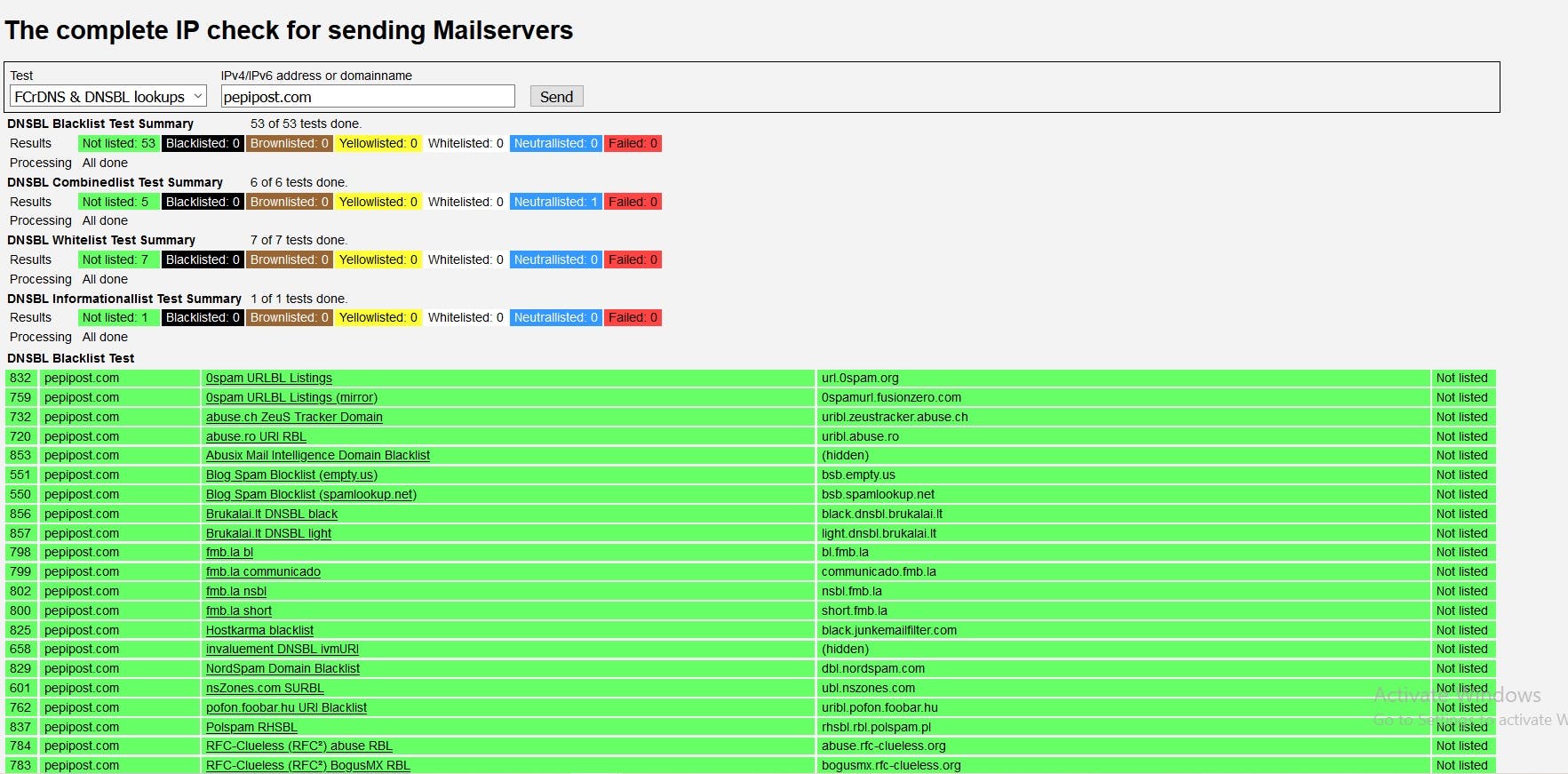
3. MXToolBox: It checks for blacklisting of your domain in multiple RBL List and provides suggestions on your domain's current status and blacklisting.
4. Third-Party blacklists: You can also check the individual lists of RBL services such as Barracuda, Spamhaus, etc. They will give you detailed information about listings.
Here are some screenshots of Spamhaus Blacklist to help you along:
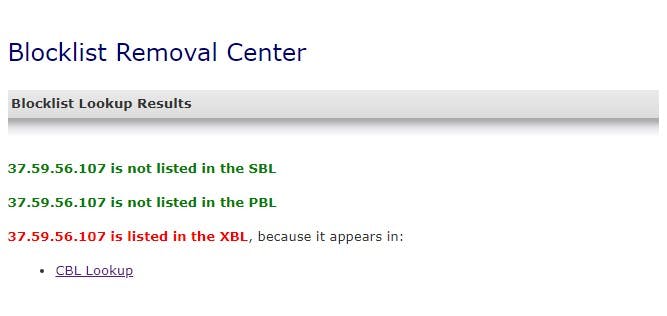
Before you request delisting of your site, you must fix the issue that got you listed in the first place. Let’s look at some of the ways to address the issues.
What got you listed on the email blacklist?
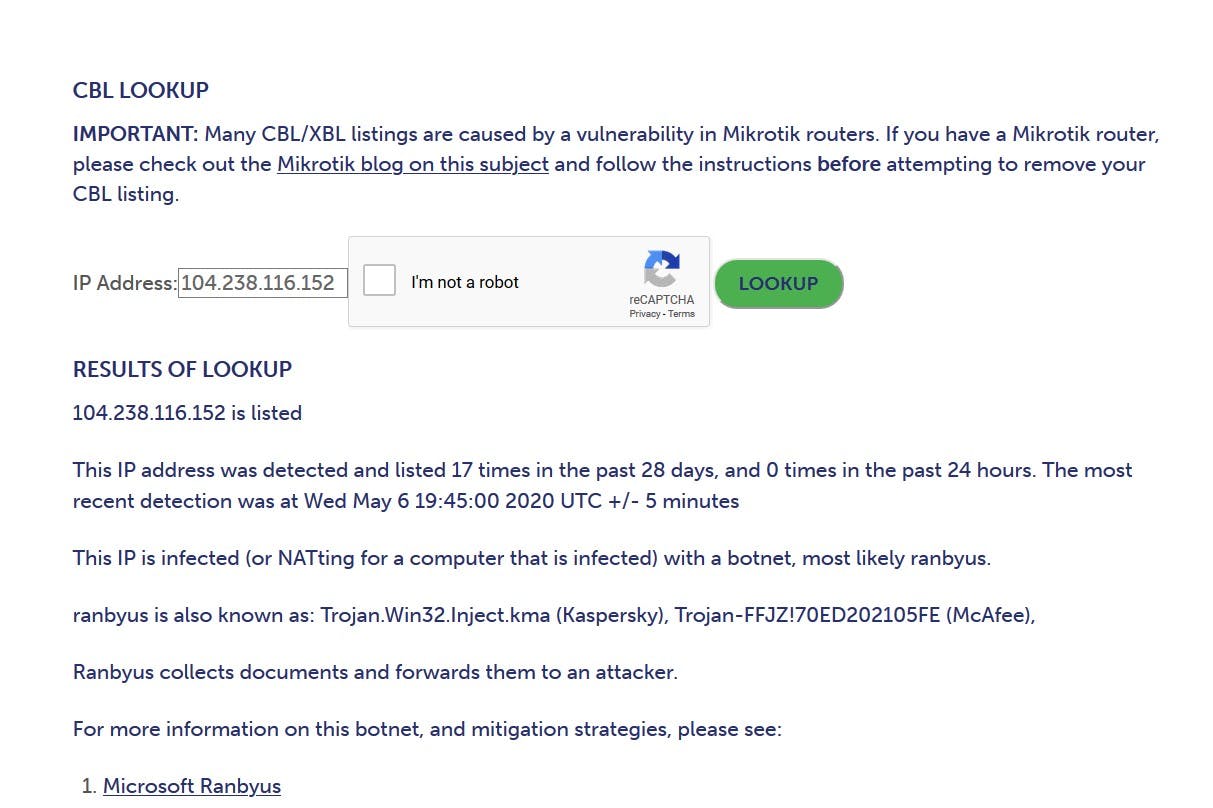
Some RBL services provide valuable insights into the reason behind your listing. Below is an example of the Spamhaus CBL blacklist lookup page to access the details you need.
Here are some of the common reasons for blacklisting.
- Email content
Your email might have:
- A spammy subject line that misrepresents the content.
- Spam words like - ‘Buy Now’, ‘Hurry’
- Full caps words - GREAT OFFER
- Unsolicited links and images and unclean HTML structure
For more info, check out our article on best email content practices
- CAN SPAM-ACT
The CAN-SPAM Act, which stands for "Controlling the Assault of Non-Solicited Pornography And Marketing Act," is a U.S. federal law enacted in 2003. It sets regulations and standards for commercial email messages, primarily aimed at reducing the volume of unsolicited and misleading email messages, often referred to as "spam.”
The violations can affect email deliverability and reputation, they are more likely to lead to higher unsubscribe rates, spam complaints, and damage to your sender reputation rather than direct blacklisting.
Here are some ways in which violations of the CAN-SPAM Act could impact your email deliverability:
- Failure to Provide an Opt-Out Mechanism
- Misleading Subject Lines
- Deceptive Header Information
- Lack of Postal/Physical Address
- Failure to Honor Opt-Out Requests
- Virus, Trojan, or Spambot infection
A Virus, Trojan, or Spambot infection refers to a computer security threat in which malicious software, also known as malware, infiltrates a computer or network with the intent to cause harm or gain unauthorised access. Here's a breakdown of these terms:
(a). Virus: A type of malware that attaches itself to legitimate programs or files and replicates when the infected program or file is executed. It can spread from one computer to another via infected files or email attachments. Viruses are designed to corrupt, steal, or delete data, and they can also be used to gain control of a computer.
(b). Trojan (or Trojan Horse): A deceptive type of malware that disguises itself as a legitimate program or file to trick users into executing it. Unlike viruses, Trojans do not replicate themselves. Once activated, Trojans can perform various malicious actions, such as stealing data, providing unauthorised access to a computer, or facilitating the installation of other malware.
(c). Spambot: A type of malware designed to send out a large volume of spam emails automatically. These emails often contain unsolicited advertisements, phishing attempts, or links to malicious websites. Spambots can infect computers and use them as part of a network, called a botnet, to distribute spam emails en masse.
Infections caused by viruses, Trojans, or spambots can have serious consequences, including data loss, identity theft, financial fraud, and disruption of computer systems. To protect against such infections, always use up-to-date antivirus software, avoid downloading or executing files from untrusted sources, and maintain good cybersecurity practices, including regular software updates and strong passwords.
- Open Relays
An ‘Open Relay’ refers to a mail server configuration that allows anyone on the internet to send email through it without requiring authentication or verification. This is a significant security vulnerability and is generally considered an undesirable configuration.
In an Open Relay system, spammers can abuse the server by using it to send large volumes of unsolicited and often malicious emails, a practice commonly known as ‘email relaying.’ This can result in the mail server being blacklisted by various email providers and organizations due to its association with spam.
To prevent Open Relay vulnerabilities, email server administrators should configure their servers to require authentication and limit relaying only to trusted users or domains. It will mitigate the risk of unauthorized use and maintain the email server’s integrity and reputation.
- Email list hygiene
Email list hygiene refers to regularly cleaning and maintaining an email marketing list to ensure that it contains only valid, engaged, and consenting recipients. It is a critical practice for email marketers to improve email deliverability, engagement rates, and overall campaign success.
How to get your email domain or IP address removed from a blacklist?

- Getting your email domain or IP address removed from a blacklist involves a series of steps.
undefinedundefinedundefinedundefinedundefinedundefinedundefinedundefinedundefinedundefined
Remember that prevention is key. By following best email marketing practices and maintaining a clean email list, you can reduce the likelihood of being blacklisted.
How to prevent being added to an email blacklist?
Here are some of the best practices:
- Avoid procuring lists from third parties. Send emails to opt-in users only.
- Remove inactive or bounced email addresses from your mailing list.
- Respect un-subscribers, don’t retarget them in your email campaigns.
- Follow the email warmup process before sending emails at scale.
- Segment your target audience and send emails accordingly.
- Don’t sell; instead, add value through your email content.
- Monitor your domain and IP reputation every 15 days.
- Don't send emails through an open relay SMTP server.
- Craft your email content to appear less like spam messages.
- Keep checking to ensure your server is free of malware or bots.
Conclusion
Follow best email marketing practices, maintain a clean email list, and promptly address any issues that may lead to blacklisting. It will ensure your domain and/or IP address remains in good standing.
If you find yourself on a blacklist, take swift and appropriate actions to rectify the problem and follow the specific delisting procedures outlined by the blacklist provider.
Remember, a proactive approach to email hygiene and compliance is the key to maintaining a positive sender reputation and ensuring your emails reach their recipients.
Excited about the latest in Bulk Email Marketing! Check out this insightful blog on Gmail and Yahoo updates in the email marketing landscape.
Explore the Blog - Here
Stay ahead of the game with valuable insights on optimizing your email campaigns! 📬
Other Related Tutorials.
Email Bounce
barracuda blacklists
spamhaus blacklist
cbl blacklist
Grade My Email
Check your spam now?
Netcorecloud's toolkit is the solution to all your email problems.

You can also explore
Netcore connects & unifies your data across all sources, connects to your marketing channels and provides you with control over AI Powered automation and personalization.
Deploy emails that are
screenshot worthy!










Hitesh Pandey💻
Full Stack Developer, Pepipost
🥑 Developer Evangelist | 🥇Email Geek